Technology
Revealed: 8093642079 – Find Out Who’s Behind the Number

Have you received a missed call or multiple rings from the number 8093642079? You’re not alone. This article is a comprehensive, expert-led guide designed to help you identify the source of that mysterious number. Whether you’re concerned about privacy, security, or simply curious, we’ve got you covered with everything you need to know.
Understanding the Mystery Behind 8093642079
You’ve probably stared at your phone wondering: “Who just called me?” That unease is totally normal—especially when the number looks unfamiliar. In today’s digital era, unknown numbers are often associated with fraud, spam, or even cyberstalking.
So what exactly? While it’s formatted like a standard Indian mobile number, its purpose remains unclear without further investigation. It might be a telemarketing firm, an automated spam bot, or even a scammer looking to bait unsuspecting users into answering.
Why Do Unknown Numbers Like 8093642079 Call You?
There’s no one-size-fits-all reason behind unexpected calls. Here are a few common causes:
-
Telemarketing Campaigns: Brands promoting new services
-
Missed or Wrong Calls: Human error still exists
-
Scam Tactics: Fake credit card alerts, job scams, or insurance frauds
-
Robocalls: Automated systems dialing multiple numbers at once
-
Social Engineering Attempts: Trying to gather your personal details
Is 8093642079 a Scam or a Legitimate Number?
Many user complaints across forums and platforms report calls from as suspicious. These calls are often characterized by:
-
Immediate disconnection after one ring
-
Silence or background noise when answered
-
Requests for OTPs, bank info, or personal data
That said, not all calls from unknown numbers are malicious. Some might be legitimate businesses or relatives with new numbers.
What to Do When You Receive a Call from 8093642079
Here’s a golden rule: Don’t answer unknown calls without screening. Use apps like Truecaller or GetContact to determine the identity. If a voicemail is left, review it carefully before calling back. Never share personal or financial data.
How to Use Reverse Lookup Tools to Investigate 8093642079
Reverse lookup tools help track the identity of a caller based on their number. Top platforms include:
-
Truecaller – Most popular but raises privacy concerns
-
Whoscall – Offers robust offline functionality
-
NumLookup – Free and straightforward
-
Whitepages – Premium service with verified info
Enter 8093642079 into these databases to check reports, caller names, or spam ratings.
Steps to Block 8093642079
Whether you’re on Android or iPhone, here’s how to block the number:
Android:
-
Open Phone app
-
Tap on the recent call from 8093642079
-
Select Block/report spam
iOS:
-
Open Phone app
-
Tap the “i” icon beside 8093642079
-
Scroll down and tap Block this caller
For extra security, enable “Silence Unknown Callers” in your settings.
How to Report 8093642079 as a Scam or Nuisance
-
TRAI’s DND (Do Not Disturb) App – Report spam in India
-
Google Phone App – Mark as spam directly
-
National Cyber Crime Portal – File official complaints
-
Facebook or WhatsApp – Block and report numbers easily
Why You Should Care About Calls from 8093642079
Numbers like 80936420 can pose more than just an annoyance. Repeated spam calls may:
-
Lead to financial loss
-
Cause stress or mental strain
-
Distract from work or personal time
-
Open doors for further privacy violations
8093642079
The number 8093642079 might appear harmless at first glance, but the ambiguity surrounding it makes it important to remain cautious. If you’ve received repeated calls, document the time and date, take screenshots, and block the number across all platforms.
Frequently Asked Questions
Is 8093642079 a spam number?
Many user reports categorize it as suspicious or spam based on call behavior and timing.
Can I trace 8093642079 for free?
Yes, using Truecaller, NumLookup, or Whoscall can help you trace the number.
Should I report 8093642079?
Absolutely, especially if you’re being harassed or the caller asks for personal information.
Will blocking 8093642079 stop all spam?
No, but it’s a good start. You should also enable call-blocking settings.
Can scammers spoof the number 8093642079?
Yes. Spoofing is common where fraudsters display fake numbers on caller ID.
Is it safe to call back 8093642079?
No. If the call was important, they’ll leave a voicemail or try again.
Conclusion
In a world where spam and scams are on the rise, staying informed about numbers like is critical. Trust your instincts, use digital tools to verify identities, and always prioritize your personal safety. Whether it’s blocking, tracing, or reporting, take control before a minor nuisance turns into a bigger threat.
Technology
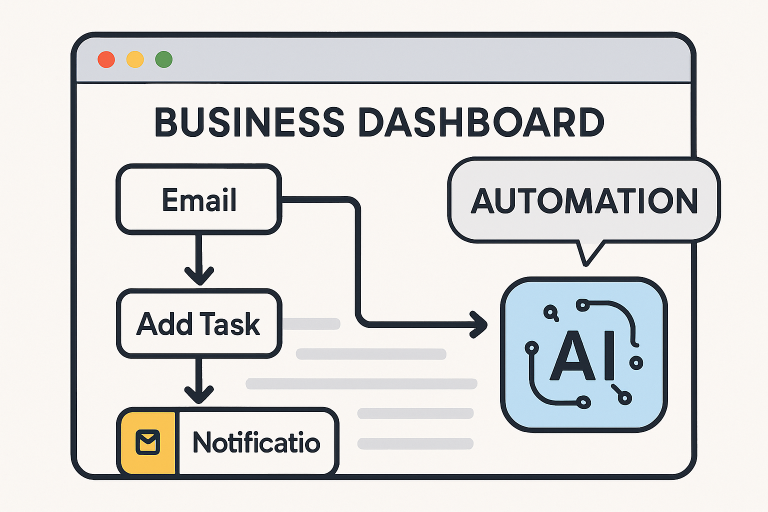
Harnessing AI Workflow Builders to Streamline Business Operations
Artificial intelligence (AI) is becoming essential for businesses aiming to enhance operations and minimize human errors. Many companies are now utilizing no-code solutions, allowing non-technical users to automate processes efficiently. AI workflow builders are at the forefront of this innovation, significantly changing how teams manage business processes by simplifying complex workflows, enabling employees to focus on growth-related tasks. These builders empower various departments, from operations to finance, to transition from manual, labor-intensive processes to streamlined, intelligence-driven operations. The integration of these workflow builders helps organizations adapt to evolving customer expectations and market shifts, a crucial aspect of digital transformation.
In conclusion, implementing AI call center software can significantly transform business operations by improving efficiency, accuracy, and customer satisfaction. Companies are reaping the benefits of these platforms, which streamline routine tasks and allow employees to focus on strategic initiatives, as detailed in resources like how to implement AI call center software. Automated workflows and data-informed decision-making not only reduce costs but also enhance consistency across multiple functions. The accessibility of low-code and no-code solutions enables organizations of all sizes and industries to adopt sophisticated AI tools, adapt to evolving processes, and maintain regulatory compliance. By thoughtfully integrating AI into core business strategies, companies foster greater innovation, resilience, and long-term operational agility.
Understanding AI Workflow Builders
AI workflow builders provide intuitive, visual interfaces enabling users to automate end-to-end business operations with little or no coding required. By dragging and dropping prebuilt elements, users can map out the steps of even highly specialized processes, embed decision-making logic, and connect workflows to external data sources. These builders typically support integrations with popular communication channels like email, SMS, web chat, and voice, enabling businesses to manage customer and internal interactions in real time.
Crucially, AI workflow builders leverage machine learning and natural language processing to automate data analysis, generate contextual responses, and deliver intelligent recommendations. These solutions are designed to replicate intricate human workflows while offering the speed and scalability of automation. The result is increased reliability, efficiency, and the ability to handle higher workloads without increasing labor costs.
Benefits of AI-Driven Automation
- Increased Efficiency: Automating repetitive processes saves significant time and energy, allowing skilled staff to dedicate more bandwidth to business-critical projects.
- Error Reduction: By standardizing repetitive workflows and leveraging data-driven decision-making, AI minimizes human errors, ensuring greater accuracy in daily operations.
- Scalability: AI workflow builders empower organizations to expand operations swiftly without requiring a matching increase in staff or resources.
- Cost Savings: Businesses can achieve notable reductions in operational expenses by automating manual tasks and reducing the need for additional headcount.
Organizations that take advantage of AI-powered automation can future-proof their businesses. This technology not only assists with current workloads but also prepares teams to adapt quickly to changes in demand or workflow, giving them an edge in competitive markets.
Key Features to Look For
- No-Code Interface: The best workflow builders feature simple, intuitive drag-and-drop tools that make it straightforward for non-developers to design new processes.
- Stateful Memory: Advanced builders maintain contextual information throughout each workflow, ensuring continuity and delivering highly personalized interactions to end users.
- Multi-Channel Integration: Robust platforms provide support for a wide range of communication and business channels, delivering a seamless experience for both customers and internal users.
- Real-Time Testing: Many workflow builders include tools for immediate testing and iteration, enabling businesses to rapidly refine and optimize their processes.
Access to powerful analytics, compliance features, and compatibility with core business software are also essential for ensuring long-term success and adaptability.
Implementing AI Workflows in Your Business
- Identify Processes for Automation: Begin with a thorough review of your operations to find repetitive, labor-intensive tasks that would benefit most from automation.
- Select the Right Tool: Evaluate various AI workflow builders to determine which aligns best with your company’s goals, industry standards, and technical requirements.
- Design and Test Workflows: Map each workflow in detail, ensuring logical consistency and operational efficiency before going live. Beta testing with select teams or use cases can reveal valuable opportunities for refinement.
- Monitor and Optimize: Use built-in analytics and feedback mechanisms to track workflow performance over time. Make incremental improvements to ensure sustained efficiency and adaptability as your business evolves.
Challenges and Considerations
Integration of AI workflow builders into existing legacy systems often necessitates custom solutions, interdepartmental collaboration, and, in some instances, external expertise. Solutions that manage sensitive data must comply with stringent cybersecurity and regulatory standards to prevent breaches and data mismanagement. Additionally, effective change management is essential when introducing automation; it requires continuous training and support to help staff adapt to new roles and processes. Establishing clear expectations and providing sufficient resources for staff education is vital for promoting a culture of innovation and ongoing improvement.
Conclusion
AI workflow builders represent a significant step toward democratizing process automation. The tools are accessible enough for non-technical staff to harness, yet powerful enough to transform entire business operations. By focusing on key features, proper implementation, and a proactive approach to change management, organizations are well-positioned to capitalize on the efficiency, cost savings, and competitive advantage that AI automation delivers.
Technology
Simpcitu : The Intersection of Internet Culture and Real Life

Simpcitu is more than just a buzzword; it’s a cultural phenomenon that has emerged from the depths of internet culture. As memes, trends, and social media interactions shape our everyday lives, Simpcitu stands at the center of it all. With its roots firmly planted in digital spaces, it influences how we communicate, date, and express ourselves in real life. This intersection between online antics and tangible experiences invites us to explore how these dynamics play out daily. As we unravel this fascinating concept, you may find yourself reflecting on your own relationship with internet culture and its implications in the world around you.
The Influence of Social Media on Real Life Interactions
Social media has revolutionized how we connect. Platforms like Instagram and Twitter have become lifelines, shaping our daily interactions.
People often turn to these platforms for validation. A ‘like’ or a comment can feel more significant than face-to-face praise. This shift influences our self-esteem and social dynamics.
While online communication fosters connections across distances, it sometimes leads to superficial relationships. Conversations that once thrived in person are now reduced to fleeting messages filled with emojis.
The art of dialogue is changing; many struggle with vulnerability in real-life encounters due to the curated nature of their online personas. Authenticity can get lost amid filters and hashtags.
Yet, there’s potential for genuine connection too. Social media allows us to share experiences, ideas, and support networks previously unimaginable in our offline lives. Balancing these worlds is increasingly vital as they intertwine seamlessly into everyday existence.
From Memes to Dating Trends: How Simpcitu Has Permeated Our Daily Lives
Simpcitu has woven itself into the fabric of our everyday interactions. It started with memes that made us laugh and reflect on modern relationships. Viral posts gave rise to a new language, connecting people through shared humor.
Dating trends have also been profoundly influenced by this online culture. Terms like “simping” have shifted perceptions about affection and vulnerability in romantic pursuits. People are redefining what it means to express interest, often leading to more open conversations around feelings.
Social media platforms serve as breeding grounds for these ideas, allowing them to spread rapidly across different demographics. Couples now navigate relationships with an awareness shaped by digital engagement.
This phenomenon isn’t limited to just dating; it influences friendships too. The way we interact is undeniably affected, blurring lines between virtual personas and real-life connections. Each post or comment contributes to how we view ourselves and others in both realms of existence.
The Positive and Negative Effects of Simpcitu on Society
Simpcitu has reshaped how communities interact. It fosters connections among like-minded individuals. People can share interests and support each other in ways that weren’t possible before.
On the flip side, it can create unrealistic expectations. Online personas often don’t match real life. This dissonance leads to disappointment, especially in relationships.
Additionally, Simpcitu contributes to a culture of instant gratification. Users expect immediate responses and validation, which can strain real-life interactions.
Mental health issues may arise as well. Constant comparison on social media platforms fuels anxiety and self-doubt for many people.
Yet, there’s potential for positive change too. Movements born from Simpcitu raise awareness about important social issues, inspiring action and community engagement.
Navigating these effects requires mindfulness and balance while enjoying the benefits of this vibrant culture surrounding us today.
Navigating Simpcitu: Tips for Maintaining a Healthy Balance Between Internet Culture and Real Life
Finding balance in the era of Simpcitu can be challenging. Start by setting boundaries for your online time. Designate specific hours to engage with internet culture, ensuring it doesn’t encroach on real-life interactions.
Engage mindfully with social media. Follow accounts that inspire or educate rather than those that drain your energy or promote negativity. Curating your feed is a simple way to enhance your mental well-being.
Prioritize face-to-face connections. Schedule regular meet-ups with friends and family, allowing genuine conversations to flourish beyond screens.
Practice digital detoxes regularly. Consider taking breaks from social platforms, even if just for a day or two each month, to recharge and refocus on personal interests outside of the digital realm.
Remember to enjoy hobbies that don’t involve technology at all—whether it’s reading a book in silence or exploring nature; these activities help ground you in reality amidst the swirling currents of Simpcitu.
The Future of Simpcitu and its Impact on the Next Generation
The future of Simpcitu is likely to evolve alongside technology and shifting societal norms. As younger generations grow up immersed in digital environments, their understanding of social dynamics will continue to be shaped by internet culture.
We can expect more nuanced interpretations of relationships influenced by online interactions. Young people might blend virtual affection with real-life connections, creating new forms of intimacy.
However, this shift could also lead to challenges. The pressure for validation through likes and shares may affect mental health. Understanding the balance between online personas and authentic selves becomes crucial.
Educational initiatives that promote healthy engagement with digital content could emerge. These programs would equip the next generation with tools to navigate both worlds confidently.
As Simpcitu continues to redefine how we connect, its impact on youth culture will unfold in fascinating ways, revealing a landscape rich in creativity yet fraught with complexities.
Conclusion:
Simpcitu has become a defining element of modern life. It embodies the fusion of online and offline interactions, shaping how we communicate and connect with one another. The influence of social media continues to expand, creating new trends that seep into our daily routines.
The effects of Simpcitu are multifaceted. On one hand, it empowers creativity and fosters community; on the other, it can lead to unhealthy comparisons and misunderstandings. Striking a balance is crucial as we navigate this ever-evolving landscape.
As we look ahead, it’s clear that Simpcitu will play an essential role in shaping future generations’ experiences with technology and culture. Understanding its nuances will help us harness its positive aspects while mitigating potential downsides.
Navigating Simpcitu requires mindfulness about our engagement levels both online and offline. By embracing authentic connections in real life alongside digital interactions, we can enrich our lives without losing touch with reality.
Technology
Profit in Motion: How Adaptive Pricing Drives Supply Chain Success
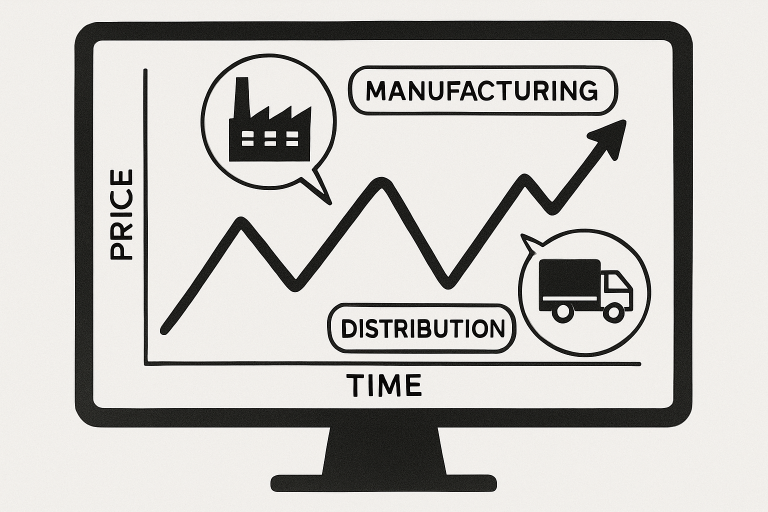
In today’s fast-moving market landscape, dynamic pricing —rapidly adjusting prices in response to demand, competition, or operational costs —is transforming the way manufacturers and distributors do business. This approach not only helps companies to maximize their revenue potential but also ensures they remain agile in the face of changing market conditions. Companies leveraging pricing software for manufacturing can more easily implement and maintain successful dynamic pricing strategies, providing a considerable competitive advantage.
The manufacturing and distribution sectors face unique challenges, including fluctuating raw material costs, intricate supply chains, and evolving customer expectations. Dynamic pricing, backed by robust analytics and technology, enables these companies to fine-tune their pricing models, capitalize on market trends, and respond more quickly to threats and opportunities. As technology and analytics become more accessible, dynamic pricing is no longer just for industry leaders—it’s a critical tool for businesses of every size. Still, implementing dynamic pricing is not without its challenges. Organizations must balance the advantages of agility and increased revenue with the risks of customer pushback, potential regulatory scrutiny, and the operational complexity of real-time price optimization. Companies that succeed are those that combine real-time intelligence with transparent communications, ensuring customers view price shifts as fair and justified.
Understanding how to collect, analyze, and act on pricing data is crucial to maximizing the value of dynamic pricing. By integrating automation, artificial intelligence, and strategic planning, manufacturers and distributors can transform dynamic pricing from a tactical exercise into a long-term growth driver
Understanding Dynamic Pricing
Dynamic pricing is a flexible approach that enables companies to respond rapidly to ever-changing factors, including demand, supply constraints, production costs, and competitor actions. In manufacturing and distribution, this means pricing products not on a fixed schedule, but in real-time, aligning price with value and market realities. This strategy is increasingly critical as customer expectations evolve and global supply chains grow more complex. The shift towards digitalization and data-driven operations gives companies unprecedented control over their pricing models—a trend highlighted by leading industry publications.
Benefits of Dynamic Pricing in Manufacturing and Distribution
- Revenue Optimization: Dynamic pricing enables capturing more value during periods of high demand, while stimulating sales when demand is low. This adaptive approach helps organizations avoid leaving money on the table during market peaks and reduces losses in downturns.
- Inventory Management: Since dynamic pricing can impact buyer behavior, it enables companies to balance inventory levels effectively, thereby minimizing costly overstocks or shortages.
- Competitive Advantage: Businesses that can align their prices to market conditions in real-time are better positioned to outpace competitors and satisfy customers who expect fair, value-based pricing.
Implementing Dynamic Pricing Strategies
Rolling out a successful dynamic pricing program involves several interconnected steps:
- Data Collection & Analysis: Gather detailed data on customer purchasing trends, competitor pricing, inventory status, and input costs. Automated tools and advanced analytics systems can turn massive data sets into actionable insights.
- Automation & AI: Implementing modern, AI-powered pricing tools enables real-time price adjustments. This automation allows companies to respond promptly to shifting market dynamics, ensuring optimal price points are maintained at all times.
- Customer Communication: Clearly and proactively share the reasoning behind pricing shifts, particularly during periods of rapid change. This transparency helps maintain customer trust and loyalty.
- Monitoring & Continuous Adjustment: Dynamic pricing is not a set-it-and-forget-it process. Regularly review performance, market feedback, and customer behavior, making data-driven adjustments to fine-tune pricing models.
Challenges and Considerations
Organizations must navigate several complex issues to ensure dynamic pricing delivers its promised benefits:
- Customer Perception: Widespread or poorly explained price changes can breed mistrust or pushback, especially among long-term partners or high-value customers.
- Ethical Concerns: It’s essential to avoid strategies that exploit necessity or lead to price gouging. Ethical boundaries and fairness must be at the core of any dynamic pricing initiative.
- Regulatory Compliance: Compliance with antitrust laws and anti-discrimination regulations is mandatory, particularly as pricing models grow more advanced and complex.
Case Studies
Real-world examples illustrate the measurable benefits of adopting dynamic pricing strategies:
- Specialty Chemical Company: Implementing a value-based dynamic pricing system, a U.S.-based specialty chemical manufacturer enhanced return on sales by three percentage points within just a year, as noted in research by McKinsey & Company. The company’s data-led approach allowed for smart, targeted price increases that reflected both product value and customer price sensitivity.
- Global Specialties Company: Following several mergers, this company introduced AI-driven analytics solutions to guide its pricing structure and boost profitability, achieving a return on sales improvement within the first year of adoption.
Future Trends in Dynamic Pricing
- AI and Machine Learning Integration: More manufacturers are shifting towards AI-driven systems that continuously analyze variables and provide faster, more accurate price updates, even factoring in variables such as projected raw material shortages or changing consumer demands.
- Sustainability-Linked Pricing: Manufacturers are introducing dynamic models that reward greener practices, like discounts for orders with lower carbon footprints or premium pricing for products with sustainable sourcing. This trend aligns with a larger movement towards ESG values throughout the global supply chain.
Conclusion
Dynamic pricing has emerged as a game-changing strategy for manufacturers and distributors seeking to thrive in a demanding and volatile marketplace. By harnessing the power of analytics, automation, and transparent communication, companies can set prices with confidence, maximizing revenue, managing inventory efficiently, and fostering lasting customer relationships. Addressing challenges related to perception, ethics, and regulation is crucial to fully realizing the promise of dynamic pricing while maintaining trust and compliance in the digital era.
-

 Business8 months ago
Business8 months agoHow Horseback Adventures Foster Connection and Wellness
-

 Technology1 year ago
Technology1 year agoDetecting AI-Generated Text: Tips and Techniques
-

 Technology1 year ago
Technology1 year agoRaterpoint: Revolutionizing Online Content Evaluation and Feedback
-

 Technology1 year ago
Technology1 year agoFDXMZ24: A Comprehensive Guide
-

 Entertainment1 year ago
Entertainment1 year agoFappelo: How to Engage with This Exciting New Phenomenon
-

 Technology1 year ago
Technology1 year agoPerchance AI | Intelligent AI Solutions for Your Business
-
 Blog1 year ago
Blog1 year agoBunkralbum: What You Need to Know About This Intriguing Concept
-

 Technology1 year ago
Technology1 year agoWriters Market: Everything You Need To Know
